iptables - basics
Introduction
Iptables is a powerful firewall tool that is used to manage and secure traffic that passes in and out of a Linux-based system. It is a fundamental component of any Linux system, and it is essential for system administrators to understand how iptables works and how to use it effectively.
How iptables Work
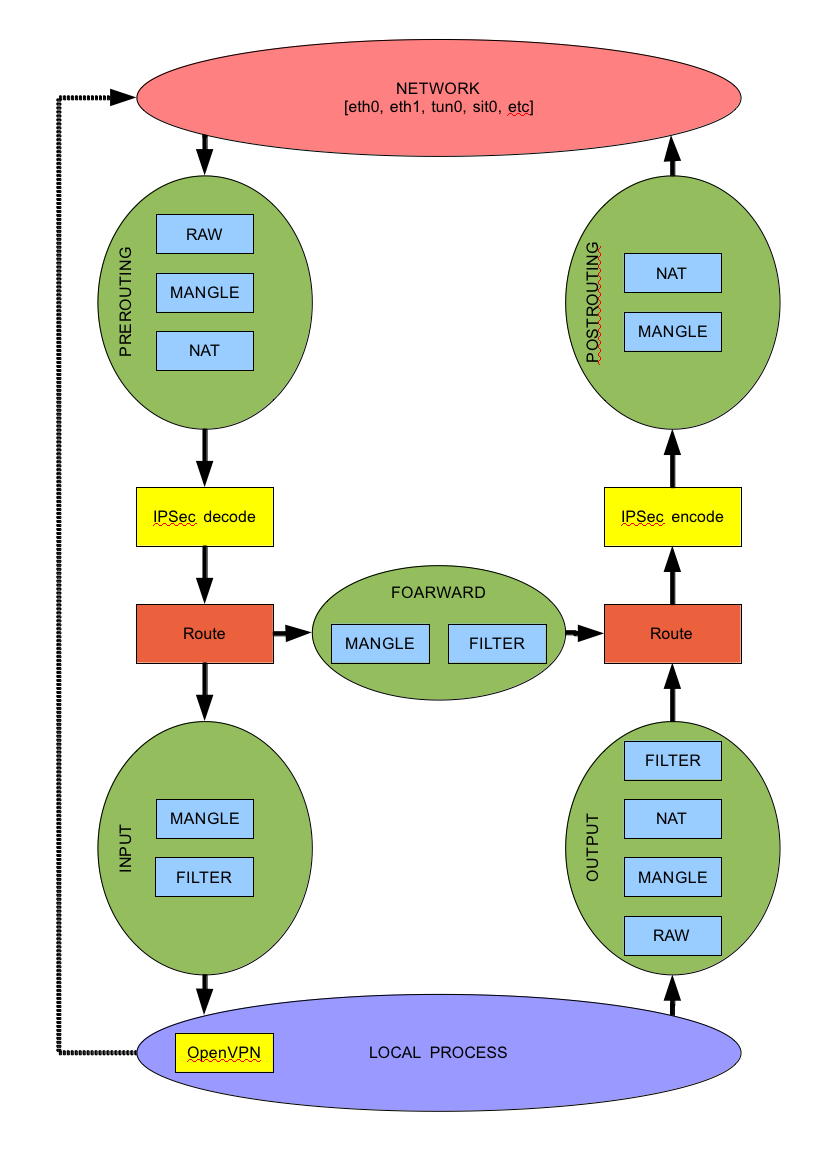
Iptables work by filtering network packets that enter, leave, or pass through a Linux-based system. It is a front-end tool for the netfilter system, which is responsible for managing network traffic. Iptables use a set of rules called chains to manage the traffic. These chains are predefined and include INPUT, OUTPUT, and FORWARD.
When a packet enters a system, it passes through the INPUT chain, which checks the packet against a set of rules. If the packet matches a rule, it is either allowed or blocked. The OUTPUT chain is for packets leaving the system, while the FORWARD chain is for packets passing through the system.
Iptables can be used to filter traffic based on various criteria such as IP addresses, ports, protocols, and more. It is a powerful tool that allows system administrators to create complex firewall rules to protect their systems.
Usage of Iptables
Iptables can be used for various purposes, including:
Security
Iptables is an essential security tool for Linux systems. It helps to protect the system from hackers, malware, and other security threats. With iptables, you can block or allow traffic based on the source, destination, protocol, or port number. By configuring iptables rules, you can create a secure network environment that is protected from external threats.
NAT
Iptables can also be used to implement Network Address Translation (NAT) on a Linux system. NAT is a technique used to map one IP address space into another by modifying network address information in the IP header of packets while they are in transit. NAT is commonly used in scenarios where multiple devices are connected to a single public IP address. With iptables, you can configure NAT rules to map incoming traffic to the appropriate internal IP addresses.
Traffic Shaping
Iptables can also be used for traffic shaping, which is the process of controlling the bandwidth usage of a network. With iptables, you can limit the speed of traffic passing through a particular port or IP address. Traffic shaping can be used to prioritize certain types of traffic, such as video or voice traffic, to ensure that they receive sufficient bandwidth.
Reference
https://www.booleanworld.com/depth-guide-iptables-linux-firewall/https://man7.org/linux/man-pages/man8/iptables.8.htmlhttps://www.netfilter.org/projects/iptables/index.htmlhttps://mdsh.com/wiki/jsp/Wiki?topic=iptables&action=action_printable