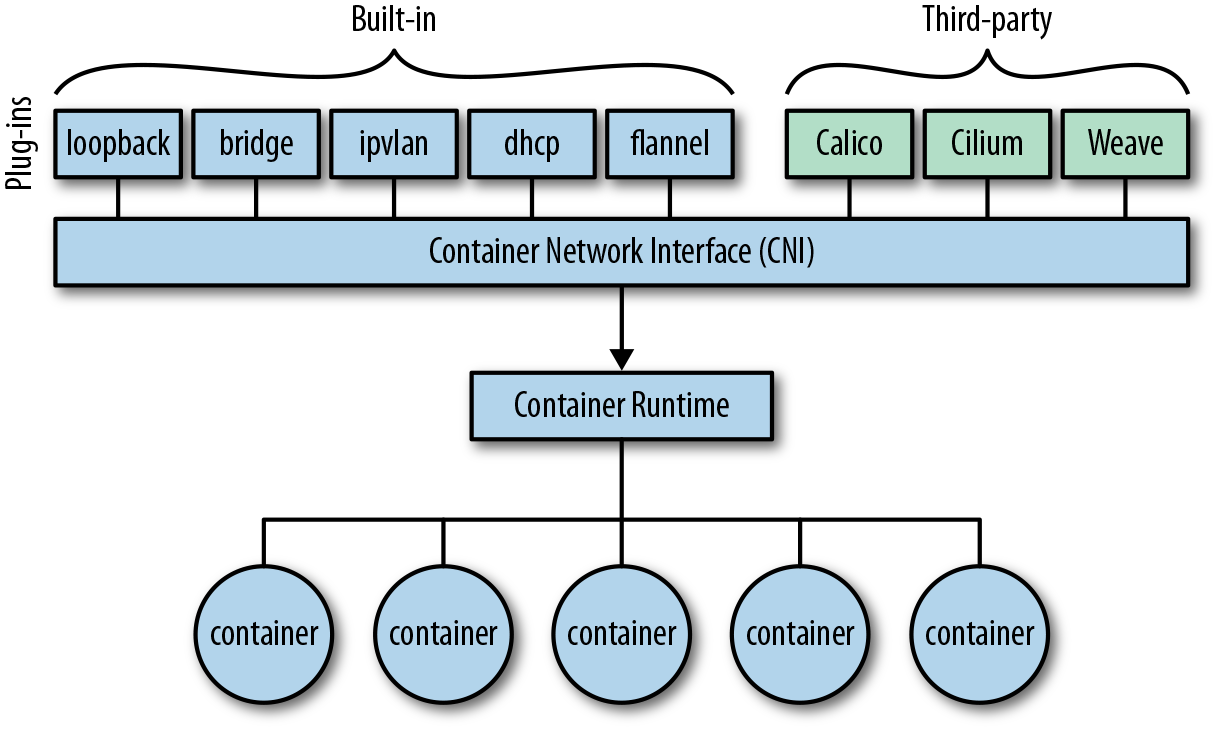
Container Network Interface (CNI) Basics
Modes for Docker Networking
- Bridge mode: Usually used for apps running in standalone containers; this is the default network driver.
- Host mode: Also used for standalone containers; removes network isolation to the host.
- Container mode: Lets you reuse the network namespace of another container.
- No networking: Disables support for networking from the Docker side and allows you to, for example, set up custom networking.
Multi-Host Container Networking
flannel
Flannel, developed by CoreOS, is a virtual network that assigns a subnet to each host for use with container runtimes. Each container, or pod in the context of Kubernetes, possesses a unique IP that is routable within the cluster. Flannel supports a variety of backends such as VXLAN, AWS VPC, and the default layer 2 UDP network. Its advantage lies in reducing the complexity of port mapping. An example of this is Red Hat’s Project Atomic, which utilizes flannel.
Weave Net
Weave Net, developed by Weaveworks, establishes a virtual network that connects Docker containers deployed across multiple hosts. Applications can utilize this network as if all the containers were connected to the same network switch, eliminating the need for port mappings and links configuration. Services offered by application containers on the Weave network can be made accessible externally, irrespective of the containers’ operational locations.
Project Calico
Metaswitch’s Project Calico utilizes standard IP routing, specifically the venerable Border Gateway Protocol (BGP) as defined in RFC 1105, and networking tools to provide a layer 3 solution. This contrasts with most other networking solutions that construct an overlay network by encapsulating layer 2 traffic into a higher layer.
Its primary operating mode necessitates no encapsulation and is specifically designed for data centers where the organization maintains control over the physical network fabric.
Open vSwitch
Open vSwitch is a comprehensive multilayer virtual switch. It’s designed to facilitate network automation through programmatic extensions, while also maintaining compatibility with standard management interfaces and protocols like NetFlow, IPFIX, LACP, and 802.1ag. It’s built to support distribution across several physical servers. Notably, it’s used in Red Hat’s Kubernetes distro OpenShift, and serves as the default switch in Xen, KVM, Proxmox VE, and VirtualBox. Moreover, it has been incorporated into numerous private cloud systems, including OpenStack and oVirt.
OpenVPN
OpenVPN, an open-source software project with a commercial option, enables you to create virtual private networks (VPNs) using TLS. These VPNs can be used to securely connect containers over the public internet.
Reference
- Container Networking, Michael Hausenblas
https://editor.networkpolicy.io/